Stolen Mount
Challenge 26: An intruder has infiltrated our network and targeted the NFS server where the backup files are stored. A classified secret was accessed and stolen. The only trace left behind is a packet capture (PCAP) file recorded during the incident. Your mission, should you accept it, is to discover the contents of the stolen data.
Solution
-
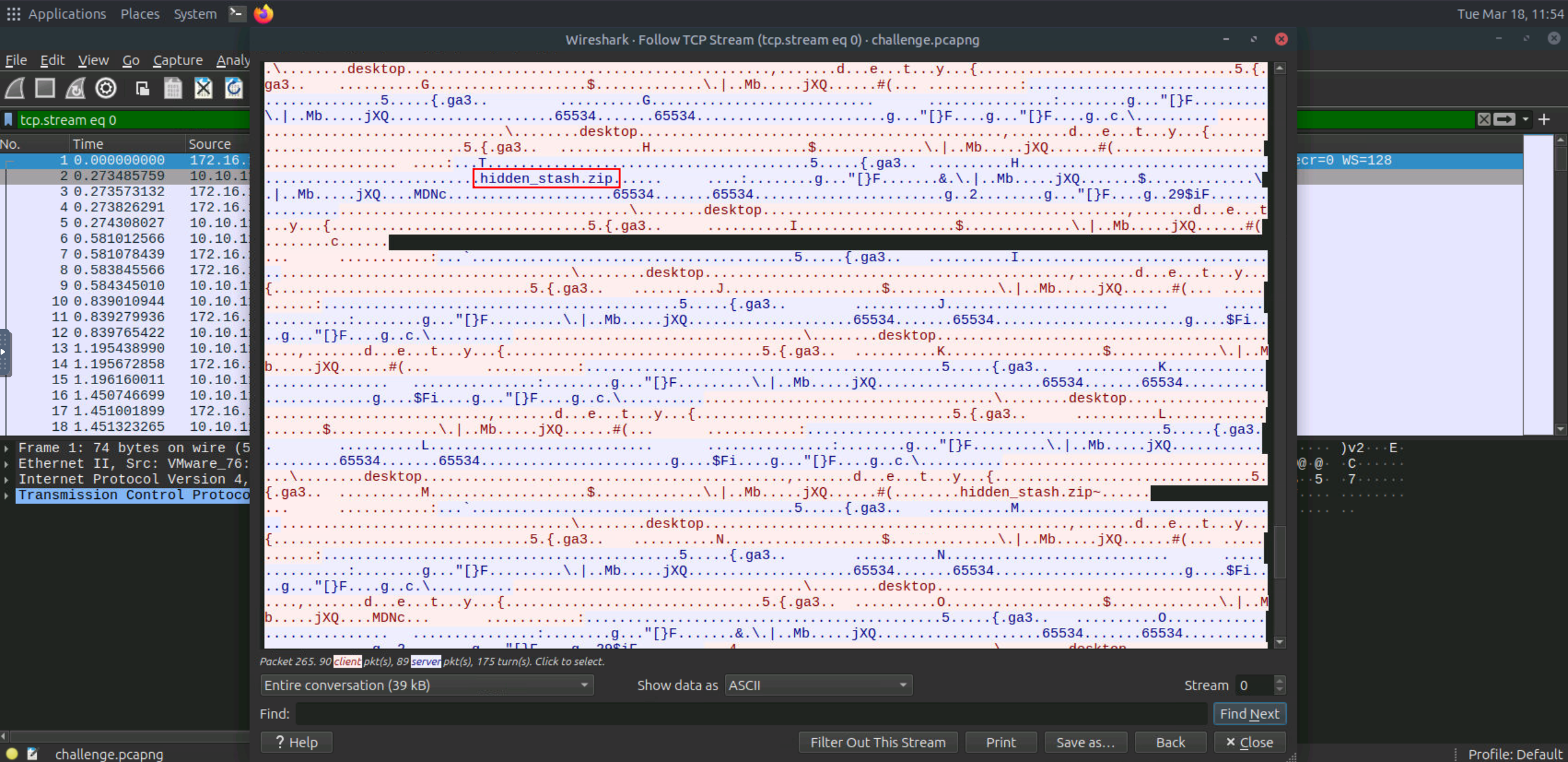
Start the machine and open the the
pcapngfile in Wireshark for analysis. -
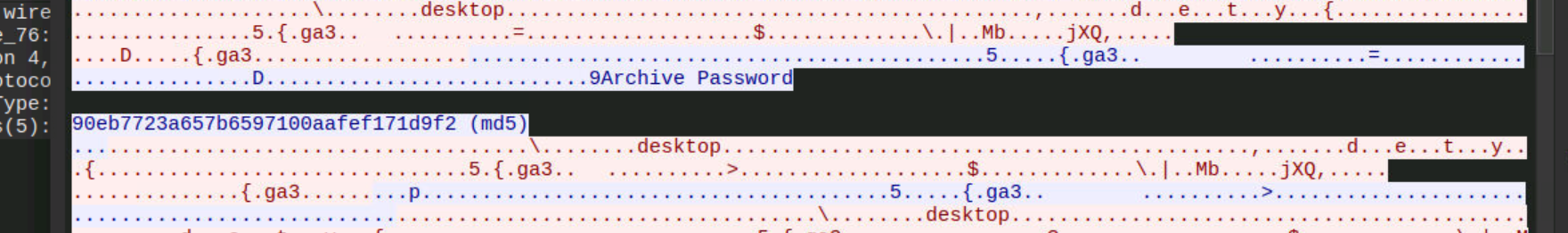
A password hash is mentioned, we crack the password using
crackstationeasily.
-
We are already provided with NFS communication. After Analyzing a bit, it is observed that
hidden_stash.zipfile is transferred being transferred.
-
Since its a zip file, we know it starts with PK (Magic bytes)
-
Copy the content of packet which starts with in raw format.
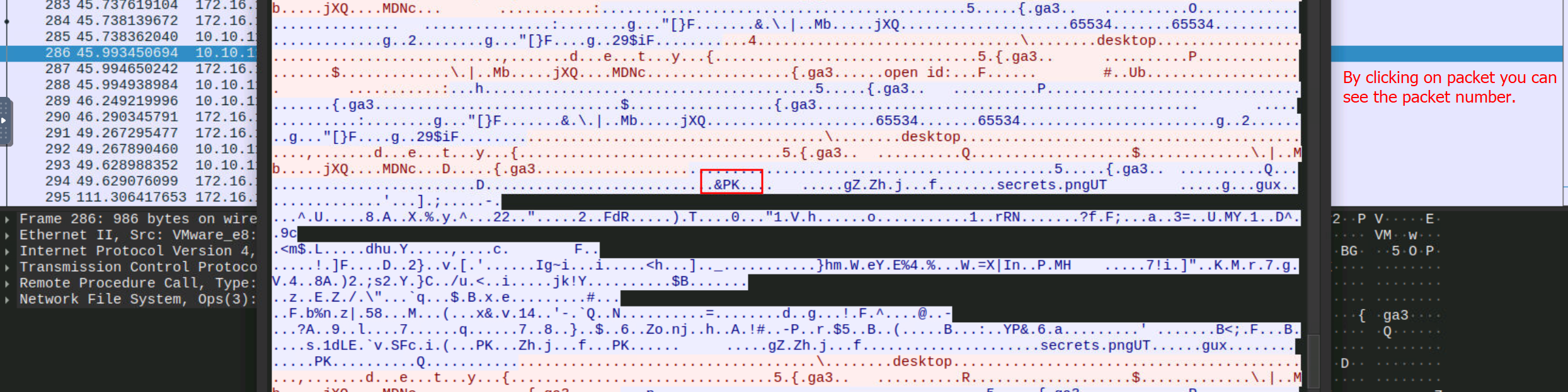
-
We need to convert the raw hex data to binary and then extract the zip.
import binascii # Read the hex dump from a file (or use a string directly) hex_data = """<Add the Raw data here>""" bin_data = binascii.unhexlify(hex_data.replace("\n", "")) with open("extracted.zip", "wb") as f: f.write(bin_data) print("ZIP file created. use unzip with password to extract its content") -
Extract the content and view the image, it is a QR code. Resolve the QR code using mobile phone. That is the answer.